How to Store Crypto Safely: Hot Wallets vs Cold Wallets Explained
- A hot wallet is connected to the internet. A cold wallet is not. That single difference defines every tradeoff between them
- $3.4 billion was stolen in crypto hacks in 2025. 62% of that came from hot wallets
- Most experienced holders follow the same rule: keep the majority of holdings in cold storage, and use a hot wallet only for amounts you actively need
- Hardware wallets cost between $50 and $250. For anyone holding more than a few hundred dollars in crypto, it is straightforward insurance
- Paybis gives you a Bitcoin wallet and a crypto wallet as part of your account. No separate setup required
Most people who buy crypto for the first time don’t think about storage. They buy on a platform, it shows up in their account, and they move on.
That works. Until it doesn’t.
In 2025, $3.4 billion in crypto was stolen through hacks, scams, and exploits. The single biggest incident was the Bybit hack in February 2025, where $1.5 billion was taken in one attack. The vast majority of losses came from wallets and platforms connected to the internet.
Where you keep your crypto matters as much as what you buy. This guide explains how hot and cold wallets work, what the real differences are, and how to build a storage setup that matches how you actually use crypto.
If you’re buying crypto and want a custodial wallet handled for you, Paybis gives you a Bitcoin wallet, a USDT wallet, and a full crypto wallet as part of your account from day one.
Table of contents
What is a crypto wallet?
A crypto wallet does not store your cryptocurrency. It stores the private keys that prove ownership and allow you to move funds on the blockchain. Lose the keys and you lose access to the crypto permanently.
The blockchain holds the actual record of who owns what. Your wallet holds the key that lets you sign transactions and prove that the record belongs to you. Think of it like the PIN to a bank account. Except there is no bank to call if you forget it.
Every wallet has a public address (like an account number you can share) and a private key (like a password you must never share). Most wallets also give you a seed phrase, a sequence of 12 to 24 words that can restore your wallet on any compatible device. This phrase is the master key to all your funds. Anyone who has it can access everything.
For a deeper look at how this works under the hood, our guide on how Bitcoin wallets work covers the full mechanics.
What is a hot wallet?
A hot wallet is any wallet that stays connected to the internet. Software wallets on your phone or browser are hot wallets. Exchange accounts are also hot wallets, managed by the platform on your behalf.
The main advantage of a hot wallet is speed. You can send, receive, and trade in seconds without any additional hardware or steps. For regular use, small purchases, transfers, and DeFi interactions, hot wallets are practical and sufficient.
The tradeoff is exposure. Because a hot wallet is always online, it is always reachable by anyone who can exploit a vulnerability in your device, browser, or the platform you use. Phishing attacks, malware, SIM swaps, and smart contract exploits all target hot wallets specifically.
That does not mean hot wallets are unsafe. It means the security of a hot wallet depends entirely on the security of the device and platform running it. A well-secured hot wallet on a clean device, with a strong password and two-factor authentication, is adequate for amounts you use day to day.
What is a cold wallet?
A cold wallet stores private keys completely offline. The keys are never exposed to the internet, which removes almost all remote attack surface. Hardware wallets are the most common form of cold storage.
When you want to send crypto from a cold wallet, the transaction is signed on the device itself without the private key ever leaving it. The signed transaction is then broadcast to the network. The key stays offline throughout.
This makes cold wallets extremely resistant to remote attacks. The February 2025 Bybit hack, where $1.5 billion was taken in a single operation, involved compromised developer infrastructure and malicious code injected into software. Cold wallets with proper setup would not have been affected because the keys never touched an online system.
The tradeoff is convenience. Sending crypto from a hardware wallet takes more steps than a software wallet. And if you lose the device without a seed phrase backup, the funds are unrecoverable.
Hot wallet vs cold wallet: how do they compare?
Hot wallets are faster and easier to use. Cold wallets are significantly more secure for larger holdings. Most serious crypto holders use both.
Here’s how the two types compare across the key dimensions:
| Feature | Hot Wallet | Cold Wallet |
|---|---|---|
| Internet connection | Always on | Offline by default |
| Setup | Instant, often free | Requires hardware ($50–$250) |
| Speed of transactions | Seconds | More steps, still fast |
| Risk of remote hack | Higher | Very low |
| Risk of physical loss | Low | Exists if device/seed not backed up |
| Best for | Active trading, small amounts | Long-term storage, larger holdings |
The comparison is not about which one is better. It is about what each one is for. A hot wallet is a spending account. A cold wallet is a safe.
What types of hot wallets are there?
Hot wallets come in three forms: exchange wallets, software wallets, and browser extension wallets. Each sits on a spectrum from most convenient to most in your control.
Exchange wallets (custodial)
When you buy crypto on a platform like Paybis, your holdings sit in a custodial wallet. The platform holds the private keys on your behalf. This is how most beginners start. It is convenient, recoverable if you lose your password, and requires no technical setup.
Paybis provides a Bitcoin wallet, a Litecoin wallet, a Tron wallet, and a USDT wallet as part of every account. For beginners who want to buy and hold without managing their own keys, this is the starting point.
The risk: you are trusting the platform’s security. Our guide on are blockchain wallets safe covers what to look for when evaluating a custodial provider.
Software wallets (non-custodial)
Applications installed on your phone or computer where you hold your own private keys. MetaMask is the most widely used for Ethereum and EVM-compatible chains. You control the keys, which means no custodial risk. The tradeoff is that if your device is compromised or you lose your seed phrase, there is no recovery option.
Browser extension wallets
A subset of software wallets that live in your browser. Useful for DeFi and Web3 interactions where you need to connect directly to decentralised applications. Subject to the same risks as any software wallet, plus browser-specific vulnerabilities.
For a full breakdown of the best non-custodial options available right now, see our guide on best non-custodial wallets.
What types of cold wallets are there?
Cold storage comes in three practical forms: hardware wallets, paper wallets, and metal seed backups. Hardware wallets are the standard for anyone holding meaningful amounts.
Hardware wallets
Physical devices that generate and store private keys offline. Transactions are signed on the device without the key ever being exposed to an internet-connected system. Most hardware wallets cost between $50 and $250 and support thousands of cryptocurrencies.
The hardware wallet market grew 31% in 2025, driven largely by the Bybit hack and growing awareness of custodial risk. Security certifications vary across devices. A secure element chip and on-device transaction confirmation are the two features most worth checking when choosing one.
For a guide to the best options currently available, bitcoin.org/en/choose-your-wallet maintains an independent, up-to-date list without commercial bias.
Paper wallets
A printed copy of your public address and private key, often as QR codes. Completely offline and immune to digital attacks. Fragile, however. Paper burns, gets wet, and fades. Best suited as a backup layer rather than a primary storage method.
Metal seed backups
Steel or titanium plates engraved with your seed phrase. Fireproof and waterproof. Used to store the recovery phrase for a hardware wallet in a location separate from the device itself. The seed phrase is the more important thing to protect. The device is replaceable; the phrase is not.
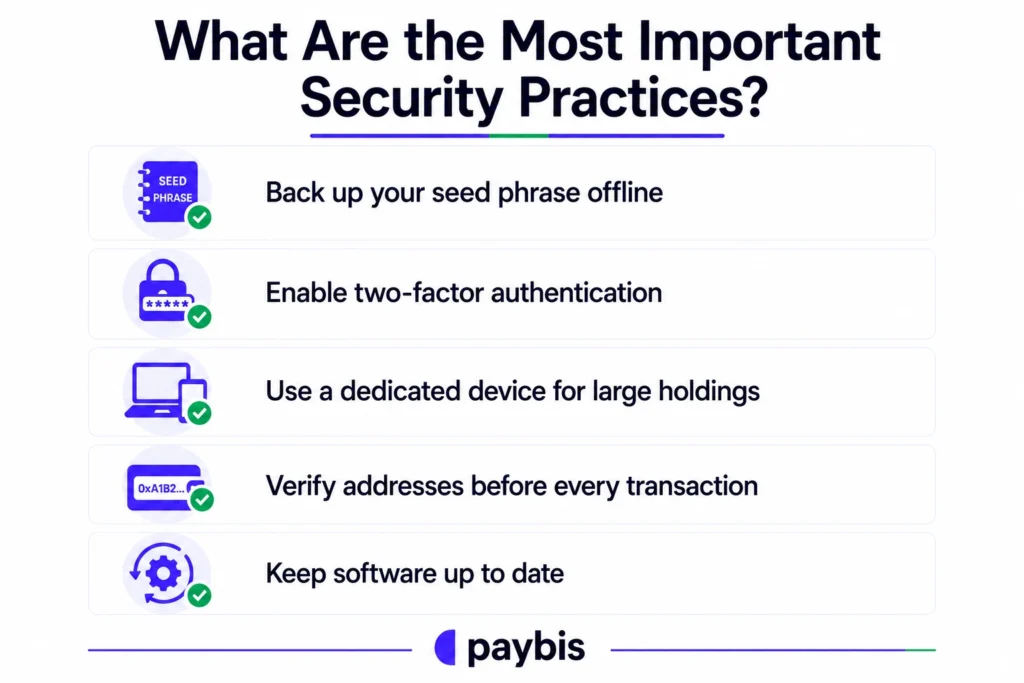
What are the most important security practices?
Whether you use a hot wallet, cold wallet, or both, five practices cover the vast majority of the risk.
Back up your seed phrase offline
Write it on paper. Store that paper somewhere physically secure and separate from your device. Never photograph it. Never type it into any website or app, regardless of what they claim. Anyone who asks for your seed phrase is attempting to steal your crypto. No legitimate platform ever needs it.
Enable two-factor authentication
Use an authenticator app (Google Authenticator or Authy) rather than SMS. SIM-swap attacks, where someone hijacks your phone number to bypass SMS verification, are one of the most common vectors for hot wallet theft. An app-based code cannot be intercepted the same way.
Use a dedicated device for large holdings
A device used only for crypto, with no other applications installed, has a much smaller attack surface than a general-purpose phone or laptop. For significant holdings, the inconvenience is worth it.
Verify addresses before every transaction
Clipboard-hijacking malware replaces copied wallet addresses with attacker-controlled ones. Always verify the first and last several characters of an address before confirming a transaction, especially for large amounts.
Keep software up to date
Exploits target known vulnerabilities. Wallet apps, operating systems, and browser extensions should be kept current. Our guide on can crypto wallets be hacked walks through the most common attack vectors and how they work.
Bottom Line
The decision between hot and cold storage is not complicated once you understand what each one is for. Hot wallets handle daily activity. Cold wallets protect long-term holdings. The two work best together, not as alternatives.
$3.4 billion was stolen in 2025. Most of it came from wallets and platforms connected to the internet. A hardware wallet costing $79 protects against almost all of that risk for anyone managing their own keys.
FAQ
Is it safe to keep crypto on an exchange?
For amounts you’re actively using or recently purchased, yes. Reputable, regulated exchanges like Paybis have security infrastructure most individuals cannot replicate independently. The risk is custodial: if the exchange has problems, your access to funds could be affected. For larger long-term holdings, moving to self-custody is the standard recommendation among experienced holders. Our guide on how custodial and non-custodial wallets differ explains the full tradeoff.
What happens if I lose my hardware wallet?
Nothing, provided you have your seed phrase backed up. The device is not where the keys live permanently. It is a tool for accessing them. As long as your seed phrase is intact and secure, you can restore full access on any compatible hardware or software wallet.
Can a cold wallet be hacked?
Remotely, it is extremely unlikely. The private key never touches an online system. The attack vectors for cold wallets are physical: someone obtaining your device and PIN, or finding your seed phrase. Physical security of your seed phrase backup is the real risk to manage with cold storage.
Do I need a separate wallet for each cryptocurrency?
No. Most modern hardware wallets and multi-chain software wallets support hundreds of cryptocurrencies from a single interface. Paybis wallets support multiple assets natively. The crypto wallet covers Bitcoin, Ethereum, USDT, Litecoin, Tron, and more from one account.
What is a seed phrase and why does it matter?
A seed phrase is a sequence of 12 to 24 words generated when you set up a wallet. It is the master recovery key for all funds in that wallet. If you lose your device or need to migrate to a new wallet, the seed phrase lets you restore full access. If someone else gets your seed phrase, they have full access too. It is the single most important thing to protect in self-custody storage.
Disclaimer: Don’t invest unless you’re prepared to lose all the money you invest. This is a high‑risk investment and you should not expect to be protected if something goes wrong. Take 2 mins to learn more at: https://go.payb.is/FCA-Info



